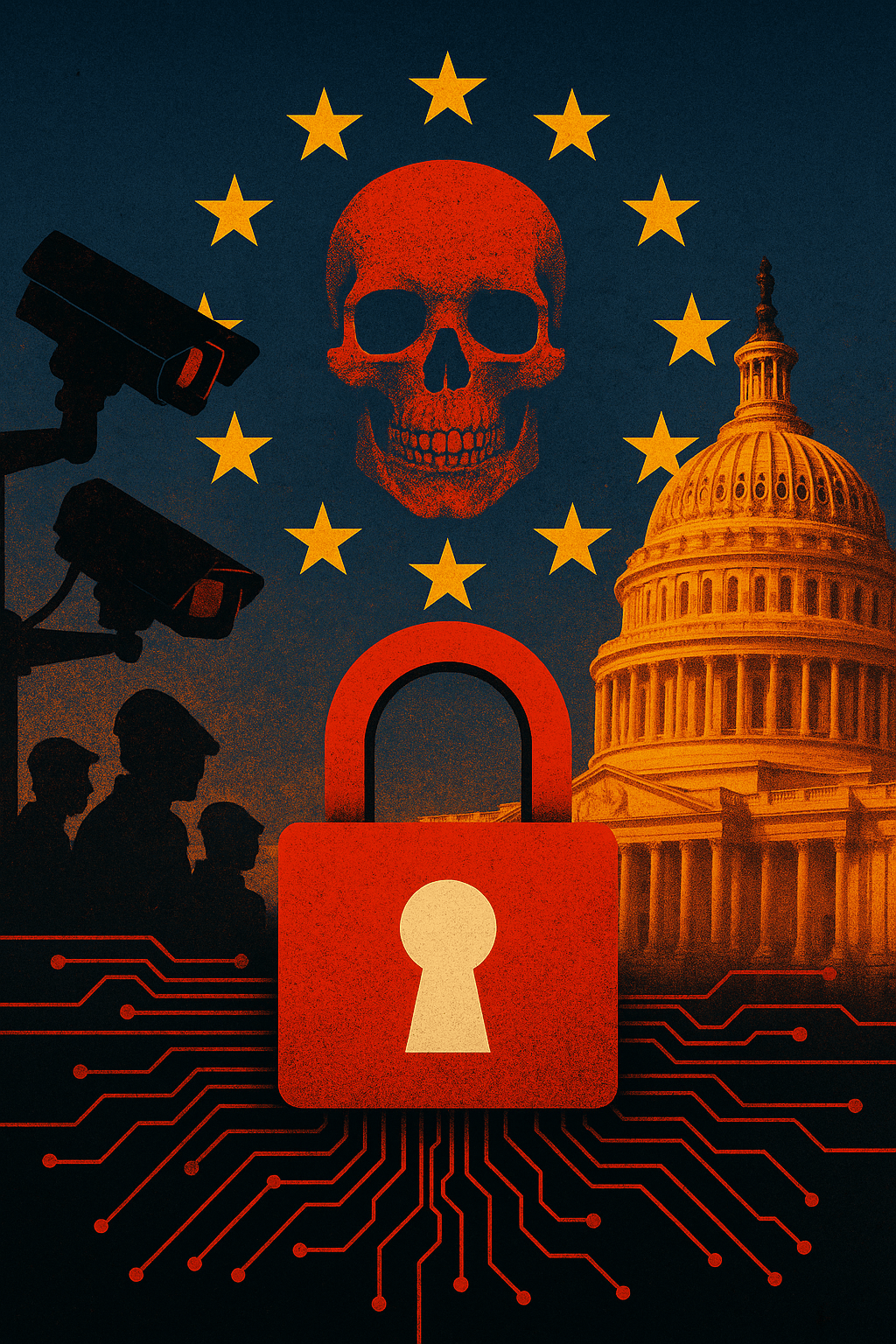
When the U.S. and EU unite to kill encryption, it’s not about stopping crime—it’s about preempting revolution. This is the digital coup beneath the façade of democracy.
By Prince Kapone | Weaponized Information
May 27, 2025
Part I – The Empire’s New Firewall: Forbes, Fear, and the Digital Dragnet
The article in question appears under the byline of Thomas Brewster, a senior technology reporter at Forbes, one of the flagship propaganda outlets of Wall Street’s ideological machine. Brewster’s journalistic portfolio is cloaked in “cybersecurity” and “digital privacy” but functions as stenography for state and corporate surveillance regimes. His beat serves empire, not truth—casting the FBI, DOJ, and Europol as protectors of the people, while framing any resistance to data colonization as a threat. Like many technocratic scribes, Brewster’s class allegiance is not to the exploited or oppressed, but to the managerial caste tasked with making digital repression appear reasonable. His employer, Forbes, is a legacy institution of imperial finance capital—currently owned by Integrated Whale Media (a Hong Kong–based investment group with deep U.S. ties), and sustained by advertising revenue from the very tech monopolies now lobbying to legalize backdoors into encrypted communication. Forbes is not a news outlet; it is a corporate-state press release machine in business-casual drag.
This agenda is echoed across institutional nodes: the FBI, whose job is to domestically discipline the internal colony; the DOJ, which constructs the legal scaffolding for repression; Europol and the European Commission, now acting as imperial junior partners; and Apple, Meta, and Google, who profit from surveillance while pretending to resist it.
What Brewster presents as a “debate” over encryption is in fact a one-sided campaign: a psychological operation wrapped in human rights rhetoric. The narrative architecture relies on classic imperial motifs—children in danger, terrorists plotting, tech firms dithering—while omitting the obvious: that the U.S. and EU are not regulating Big Tech to protect the people, but to make it more efficient at spying on them. The article’s sleight of hand is in how it collapses privacy and criminality, subtly equating the defense of encryption with complicity in abuse. This is not journalism. It’s counterinsurgency prose. Brewster invokes the specter of online harm to justify unprecedented state access to private communication, while never mentioning that the NSA and GCHQ already operate vast illegal surveillance networks. The framing erases the actual victims: journalists, organizers, and everyday people in the Global South whose survival depends on evading Western surveillance infrastructure.
The article reads like a digital-age update of the old colonial playbook: manufacture a crisis, weaponize morality, and offer empire as the solution. But behind every “child safety” initiative lies a blueprint for total information control. Brewster is not exposing threats to public safety—he is helping manufacture the consent needed to criminalize digital self-defense. And in the world being built, encryption is not a luxury—it’s a lifeline.
Part II – Encryption Is Not the Threat: Contextualizing the Digital Siege
Let’s pull the thread of reality from the tangled mess of imperial spin. Thomas Brewster’s article references a transatlantic initiative, involving the FBI, the DOJ, and Europol, aimed at pressuring Big Tech—particularly Apple, Meta, and Google—to “comply” with state efforts to access encrypted communications. It highlights recent European legislative attempts such as the EU’s proposed CSAM (Child Sexual Abuse Material) Regulation, which seeks to mandate scanning of private messages, and the U.S. EARN IT Act, which would gut Section 230 protections for encrypted platforms. These are not isolated proposals. They are synchronized moves in a broader campaign to criminalize privacy and centralize data extraction under the guise of public safety.
The article mentions fears over encrypted messaging apps such as Signal and WhatsApp, which currently offer end-to-end encryption—a feature long detested by intelligence agencies that regard secrecy for the masses as a form of rebellion. Europol is quoted demanding that “access to data must be lawful, targeted, and proportionate.” But in practice, this language is weaponized ambiguity. In every colonial and counterinsurgency context—from Ireland to Iraq—“proportionality” has always meant whatever the empire says it means.
To understand this crackdown, we must trace its structural origin. Encryption is a technical expression of sovereignty. It shields communication, organizes resistance, and enables autonomy. In the Global South, encrypted apps are used to expose corruption, resist police violence, evade surveillance, and coordinate mutual aid. In Palestine, Burma, Sudan, and Haiti, encrypted networks are not conveniences—they are tools of survival. Western imperial powers understand this. That’s why they are moving not just to regulate encryption, but to dismantle it as a form of civilian self-defense.
But this isn’t just about the periphery. The crisis is boomeranging back to the imperial core. The post-COVID capitalist state has entered an era of managed collapse—ecological, financial, and political. To stabilize itself, it must discipline its own labor force while preempting revolt. Technofascism is the emerging form of this stabilization: the fusion of finance, surveillance, and state violence, optimized for austerity and mass pacification. Encryption stands in the way. It is a crack in the digital Panopticon, and cracks must be sealed.
The campaign to end end-to-end encryption is therefore not about protecting children or thwarting terrorism—it’s about foreclosing the possibility of insurgency. The fact that both the EU and U.S. are coordinating this effort is not surprising. Atlanticism, despite its façade of liberalism, has always functioned as a unified imperial command structure. From NATO’s bombing of Yugoslavia to coordinated sanctions on Venezuela, it is the military-diplomatic expression of Western capital’s collective interests. And in the digital age, its priority is control.
Notably absent from Brewster’s article is any mention of the actual surveillance systems already in place: the NSA’s XKEYSCORE, GCHQ’s Tempora, Israel’s NSO Group, and Palantir’s predictive policing tools. The piece offers no reflection on how mass data collection has already been used to profile Black communities, target Indigenous land defenders, or algorithmically suppress protests. Nor does it question the track record of the very institutions now claiming the moral high ground. The FBI ran COINTELPRO. The DOJ oversaw the legal justifications for torture. Europol has collaborated with Frontex in the mass repression of refugees. These are not defenders of democracy. They are the administrators of colonial order.
We must also contextualize the role of corporate power. Apple, for all its posturing, is not a champion of privacy. It has routinely complied with U.S. subpoenas, geofencing requests, and iCloud surveillance mandates. Meta (formerly Facebook) collaborates with NATO-linked think tanks to police “disinformation.” Google, which began as a DARPA project, now runs the data centers that power both the Pentagon and predictive policing. Their “resistance” to backdoors is a negotiation tactic—not a principled stand.
In sum, what we are witnessing is not a debate, but a digital coup. A counterinsurgency campaign waged in cyberspace. Its goal is simple: eliminate the last frontier of digital autonomy before the next rebellion can organize. Encryption is being framed as the problem, because in a world built on extraction, opacity from below is always viewed as a threat.
Part III – Encryption as a Weapon of the Weak: Reframing the Digital Battlefield
Let us be absolutely clear: encryption is not a luxury. It is a modern shield in an ancient war. It is the digital evolution of the slave breaking his chains, the guerrilla fighter in the mountains using coded signals, the colonized journalist dodging surveillance to publish the truth. It is not the domain of criminals—it is the inheritance of every people who have ever resisted empire.
The real threat to empire is not terrorists or traffickers—it is consciousness. It is political memory preserved in messages the NSA can’t read. It is organizing meetings coordinated without the FBI listening. It is digital pamphlets distributed without the CIA knowing who clicked the link. In the colonial world, to speak freely is subversion. To organize in private is sedition. Encryption, therefore, is revolutionary self-defense.
What Brewster and the technocrats fear is not a technological feature—it is what that feature enables: a new kind of insurgency. A world in which communication is decentralized, surveillance is defeated, and mass movements are coordinated without permission. From the streets of Santiago to the jungles of Mindanao, encrypted apps have already facilitated general strikes, revolts, and mass defiance. The empire knows this. That is why it is moving to outlaw the tool, rather than address the grievances.
We must reject the lie that the state can be trusted with “targeted access.” The colonial state has never operated in good faith. There was nothing “proportionate” about the genocide of Native nations. Nothing “lawful” about COINTELPRO. Nothing “balanced” about drone strikes in Yemen or predictive policing in Chicago. The same state now demanding digital keys once ran death squads in El Salvador and wiretapped MLK.
And let us reject the liberal illusion that Big Tech will save us. Apple may refuse to build backdoors today, but it built the walled garden in which those backdoors will be hidden tomorrow. Meta may resist surveillance orders publicly while filtering Palestinian voices through “content moderation” in private. Google may encrypt your inbox, but it is mapping your brain through behavioral data and selling it to the Pentagon. These are not allies. They are junior partners in the empire.
Reframing this struggle means identifying the real lines of battle. This is not a debate about balancing safety and privacy. It is a war between those who wish to remain free and those who demand to be your master. Between the enslaved who crafted whisper networks to resist the lash and the technocrats crafting algorithms to simulate the whip. Encryption is not neutral—it is partisan. It sides with the oppressed.
That’s why every revolutionary movement—from Indigenous land defenders in Canada to peasant unions in India—must treat digital security as a political necessity. It is not enough to have a manifesto. You must protect it. It is not enough to plan rebellion. You must shield it from digital sabotage. The era of open surveillance means the era of clandestine organizing must return—not as paranoia, but as protocol.
In this reframing, we must reposition encryption not as a consumer right but as a political right. A right to resist. A right to rebel. A right to organize without the empire reading over your shoulder. And we must recognize every attempt to ban, weaken, or regulate it as a direct attack on the ability of the colonized to fight back.
The working class has no homeland in the empire’s cloud. Our loyalty is to one another, not to Amazon servers or NSA auditors. To reframe encryption is to say plainly: this is our radio in the jungle, our fire signal from mountaintop to valley. It is our whisper across prison walls. And it must be defended like a weapon, because in the digital age—it is.
Part IV – Mobilization: Digital Defense is Class Struggle
Encryption is not just code. It is class struggle. And the war on encryption is a war on the capacity of the oppressed to organize, to resist, and to survive in a world rigged for surveillance and silence. It is not abstract. It is not theoretical. It is concrete and urgent. What they want is simple: to criminalize resistance before it breathes. To intercept rebellion before it forms. To regulate dissent out of existence.
That is why our response must be just as deliberate, just as grounded, and just as international. We must treat the defense of encryption not as a technical issue for engineers but as a revolutionary imperative for the masses. This is not about privacy for the privileged—it is about survival for the targeted.
1. Ideological Unity: No Compromise on Digital Autonomy
We unite with all those who recognize that encryption is not a crime—it is a shield. From Indigenous resistance camps to Black abolitionist formations, from union organizers in Amazon warehouses to journalists exposing genocide—encryption has been vital. It has preserved lives. It has enabled struggle. And it must be defended uncompromisingly.
We declare firm ideological unity with digital freedom groups like Tor Project, Signal Foundation, and Privacy International—not because they are flawless, but because they stand on the front lines. We honor the sacrifices of whistleblowers and hackers, from Edward Snowden to Reality Winner to the Anonymous networks that disrupted empire’s data pipelines. Every byte liberated from surveillance is a blow struck for the people.
2. Historical Lineage: From Ciphers to Secure Servers
From the coded language of enslaved Africans planning escape, to the radio communications of the Viet Cong, to the zapatista communiqués from the jungles of Chiapas—secrecy has always been a prerequisite for liberation. Encryption is simply the digital continuation of that tradition. It belongs to the people. The colonial state cannot be trusted to define or regulate it.
Let us remember: the U.S. government hunted Assata Shakur, tortured Julian Assange, assassinated Qassem Soleimani, and labeled domestic dissenters as terrorists. This regime does not want safety—it wants obedience. Any regulation it proposes is prelude to repression.
3. Concrete Actions: From Resistance to Rebuild
- Adopt secure digital practices: Encourage Signal, ProtonMail, Tor, and peer-to-peer encrypted tools in all revolutionary spaces.
- Popularize digital security education: Hold workshops, create infographics, and circulate zines teaching everyday people how to encrypt, anonymize, and defend their data.
- Resist surveillance infrastructure: Mobilize against “smart” city plans, predictive policing software, biometric ID systems, and digital ID mandates being pushed under the guise of modernization.
- Build anti-surveillance coalitions: Unite technologists, trade unions, tenant groups, abolitionists, students, and land defenders under one banner: Digital Autonomy Now.
- Defend whistleblowers: Demand full amnesty for Julian Assange, Chelsea Manning, and others who exposed the empire’s digital war machine.
4. Toward a Revolutionary Digital Vanguard
The revolution will not be tweeted—but it will be encrypted. And those who build and defend secure communications will play a decisive role in the next stage of global struggle. We must begin building a revolutionary digital infrastructure—open-source, decentralized, resistant to co-optation, and accountable to the masses.
This includes revolutionary media, clandestine organizing platforms, anti-surveillance training schools, and secure counter-networks outside of Western-controlled cloud servers. It also means exposing and dismantling U.S.-backed attempts to install surveillance regimes in the Global South under the guise of “tech development.”
Let it be known: the war on encryption is a war on insurgency. It is a preemptive strike against the revolution. And we must respond accordingly—not just with condemnation, but with countermeasures.
Encryption is not a privilege. It is our duty. It is our right. It is our firewall against fascism.
In the age of technofascism, to encrypt is to resist. To code is to conspire. And to conspire for the freedom of the oppressed is the highest form of loyalty—to the people, to the planet, and to the future.
Leave a comment